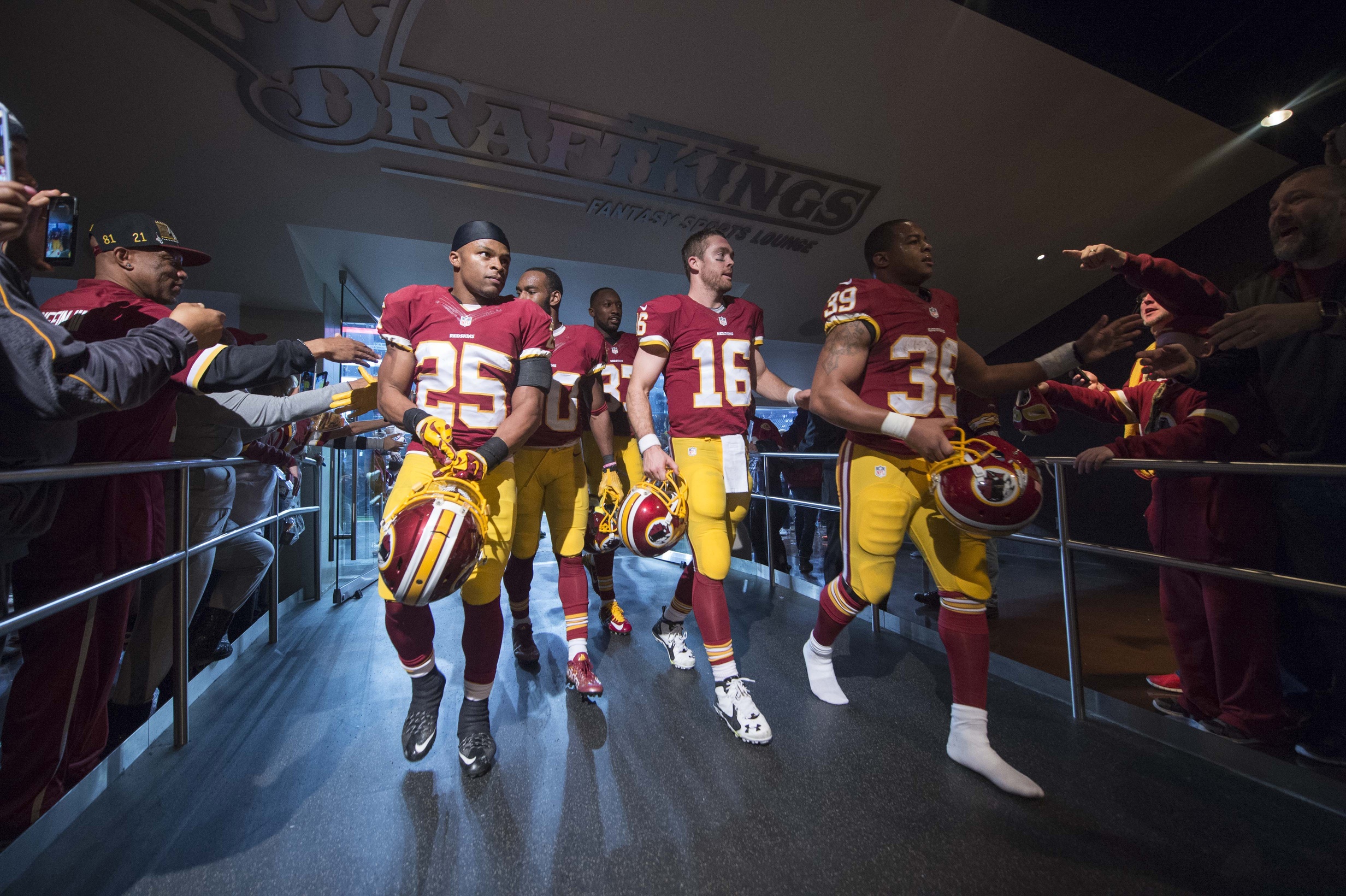
It is a lot easier to steal a laptop than it is to hack into a corporate database. The Internet erupts every time a hacker compromises data of millions of customers, but it remains silent when a laptop containing data of thousands of employees is stolen. However, that is not the case when an athletic […]
The One (Laptop) That Got Away